A random person on lemmy. Banner art from Deemo switch version
Alt lemmy @[email protected]
Alt kbin: @[email protected]
FMHY (archive): @[email protected]
- 7 Posts
- 9 Comments

 0·3 months ago
0·3 months agoUpdate regarding virtual files has more quirks.
- You cannot move files or folders. If you try nextcloud will simply copy the files to new destinaiton while not moving.
- the nextcloud sync and virtual files refresh/update independently (a change may propigate to sync but not files and vice versa).
Also turns out the reason it was a github release was it is still in alpha 😅 .

 1·3 months ago
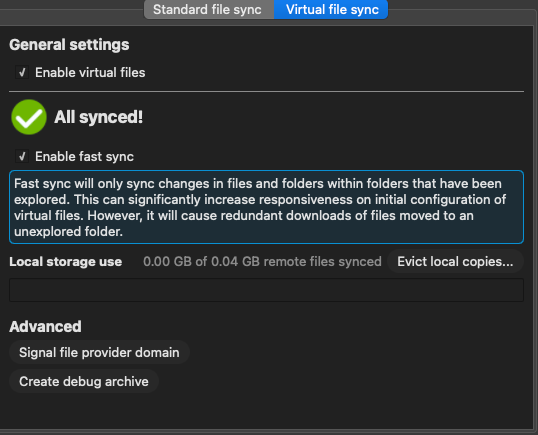
1·3 months agoUpdate the stable client does have proper virtual file sync.
Regarding the previous virtual file sync system (.nextcloud) you had to enable experimental features to get it. The latest stable just has both versions of syncing and I missed the obsious vfs sync option.
The only downside to the new system is there isn’t a make file/folder available offline always option in the context menu (you can get around this by manually setting up synced folders but it is a little inconvient).

 1·3 months ago
1·3 months agoNextcloud desktop client 3.13.0
Edit 2:
You need to grab the release from https://github.com/nextcloud-releases/desktop/releases/tag/v3.13.0
Specifically the vfs version Nextcloud-3.13.0-macOS-vfs.pkg
brew doesn’t really work

 0·3 months ago
0·3 months ago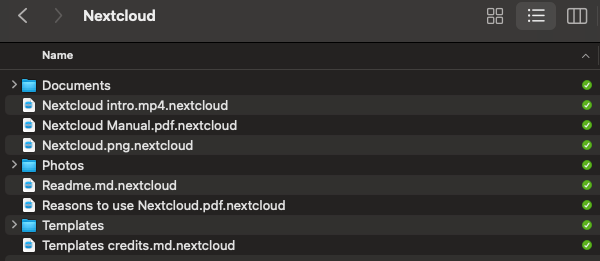
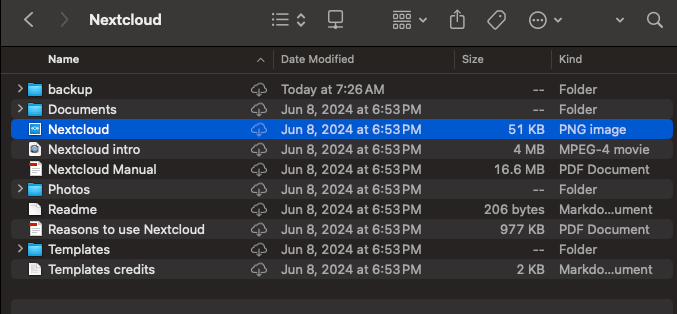
This is how it shows up for me on Nextcloud desktop client 3.13.0

 0·3 months ago
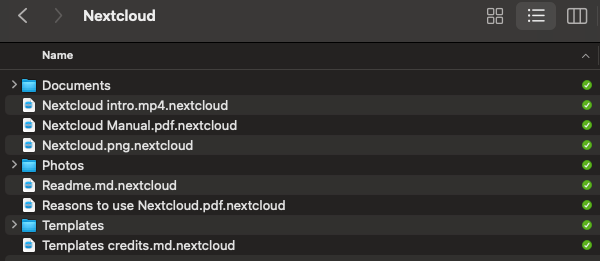
0·3 months agoUnfortunatly like syncthing nextcloud mac app also has the same file extension sync issue (they use .nextcloud).

 2·4 months ago
2·4 months agoSorry about that (didn’t think that far when making the post 🫠 ).
I updated the title

 2·4 months ago
2·4 months agoremote UI connection passes through the Home Assistant Central servers, the Central servers could maintain that safety database and off switch
I think this is how home assistant handles it. When they put out a cve they can update the insecure version list which makes nabucasa refuse remote forwarding (until you update).
Initially I was just thinking if a open-source project is on github and uses the security disclosure feature if it would be possible to pull data from it and disable remote acess (either by auto shutting down the service or simply disabling routing on a reverse proxy).
Having a system that does without a security disclosure list from a project maintainer would be far mor difficult like having the proxy disable one of your services if it detects a vulnerability in a dependency.

 4·4 months ago
4·4 months agodata source for these vulnerabilities
Are you refering locations for vulnerability disclosure or are you more referring to bug bounty?
Personally, I’d just put everything behind a VPN. The attack surface is much smaller.
Fair enough

I do own a cheap numerical xyz domain (something like 432433.xyz) cost a dollar per year. Only reason I was curious about eu.org is its very short and ends with .org.
I haven’t really bought a proper .com domain since I’m just using them for side hobby projects (not for sharing with other people).